A company has HPE Aruba Networking APs (AOS-10), which authenticate clients to HPE Aruba Networking ClearPass Policy Manager (CPPM). CPPM is set up
to receive a variety of information about clients ' profile and posture. New information can mean that CPPM should change a client ' s enforcement profile.
What should you set up on the APs to help the solution function correctly?
Your company wants to implement Tunneled EAP (TEAP).
How can you set up HPE Aruba Networking ClearPass Policy Manager (CPPM) to enforce certificated-based authentication for clients using TEAP?
A company requires a centralized audit trail for commands that managers enter on AOS-CX switches.
What can you set up on the switches to meet this requirement?
You need to set up HPE Aruba Networking ClearPass Policy Manager (CPPM) to provide certificate-based authentication of 802.1X supplicants.
How should you upload the root CA certificate for the supplicants ' certificates?
You need to set up an HPE Aruba Networking VIA solution for a customer who needs to support 2100 remote employees. The customer wants employees to
download their VIA connection profile from the VPNC. Only employees who authenticate with their domain credentials to HPE Aruba Networking ClearPass Policy
Manager (CPPM) should be able to download the profile. (A RADIUS server group for CPPM is already set up on the VPNC.)
How do you configure the VPNC to enforce that requirement?
Refer to the exhibit.
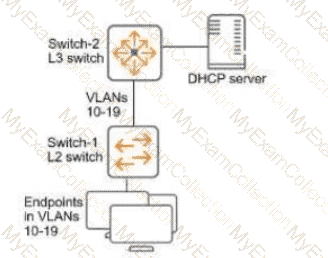
You have verified that AOS-CX Switch-1 has constructed an IP-to-MAC binding table in VLANs 10-19. Now you need to enable ARP inspection for the endpoint connected to Switch-1. What must you do first to prevent traffic disruption?
A company has a variety of HPE Aruba Networking solutions, including an HPE Aruba Networking infrastructure and HPE Aruba Networking ClearPass Policy
Manager (CPPM). The company passes traffic from the corporate LAN destined to the data center through a third-party SRX firewall. The company would like to
further protect itself from internal threats.
What is one solution that you can recommend?
Refer to the exhibits.

You are setting up HPE Aruba Networking ClearPass Policy Manager (CPPM) to authenticate wireless clients with EAP-TLS and 802.1X. CPPM should assign clients to an AOS firewall role named contractors-fullaccess if the clients meet these requirements:
AD account is enabled: AccountStatus 512
Security group name is Contractors
What should you do to make these policies meet these requirements?
You have set up a mirroring session between an AOS-CX switch and a management station, running Wireshark. You want to capture just the traffic sent in the
mirroring session, not the management station ' s other traffic.
What should you do?
You manage AOS-10 APs with HPE Aruba Networking Central. A role is configured on these APs with the following rules:
Allow UDP on port 67 to any destination
Allow any to network 10.1.6.0/23
Deny any to network 10.1.0.0/16 + log
Deny any to network 10.0.0.0/8
Allow any to any destination
You add this new rule immediately before rule 2:
Deny SSH to network 10.1.4.0/23 + denylist
What happens when a client assigned to this role sends SSH traffic to 10.1.11.42?
A company is implementing HPE Aruba Networking Wireless IDS/IPS (WIDS/WIPS) on its AOS-10 APs, which are managed in HPE Aruba Networking Central.
What is one requirement for enabling detection of rogue APs?
You are setting up an HPE Aruba Networking VIA solution for a company. You have already created a VPN pool with IP addresses for the remote clients. During
tests, however, the clients do not receive IP addresses from that pool.
What is one setting to check?
Refer to Exhibit:
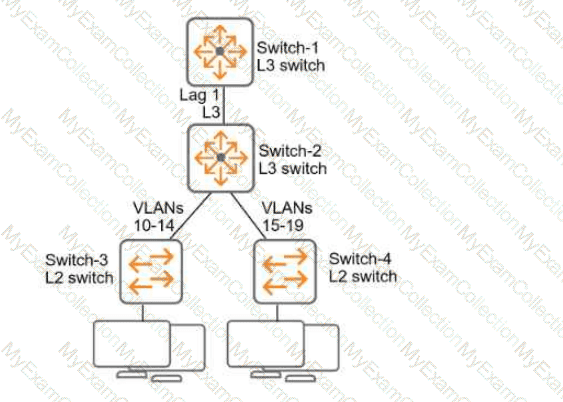
All of the switches in the exhibit are AOS-CX switches.
What is the preferred configuration on Switch-2 for preventing rogue OSPF routers in this network?
You need to set up HPE Aruba Networking ClearPass Policy Manager (CPPM) to provide certificate-based authentication of 802.1X supplicants. How should you upload the root CA certificate for the supplicants’ certificates?
A company has HPE Aruba Networking APs and AOS-CX switches, as well as HPE Aruba Networking ClearPass. The company wants CPPM to have HTTP User-
Agent strings to use in profiling devices.
What can you do to support these requirements?
You are setting up policy rules in HPE Aruba Networking SSE. You want to create a single rule that permits users in a particular user group to access multiple applications. What is an easy way to meet this need?
A security team needs to track a device ' s communication patterns and identify patterns such as how many destinations the device is accessing.
Which Aruba solution can show this information at a glance?
A company wants to use HPE Aruba Networking ClearPass Policy Manager (CPPM) to profile Linux devices. You have decided to schedule a subnet scan of the devices ' subnets. Which additional step should you complete before scheduling the scan?
You need to create a rule in an HPE Aruba Networking ClearPass Policy Manager (CPPM) role mapping policy that references a ClearPass Device Insight Tag.
Which Type (namespace) should you specify for the rule?
You have installed an HPE Aruba Networking Network Analytic Engine (NAE) script on an AOS-CX switch to monitor a particular function.
Which additional step must you complete to start the monitoring?
Refer to Exhibit.
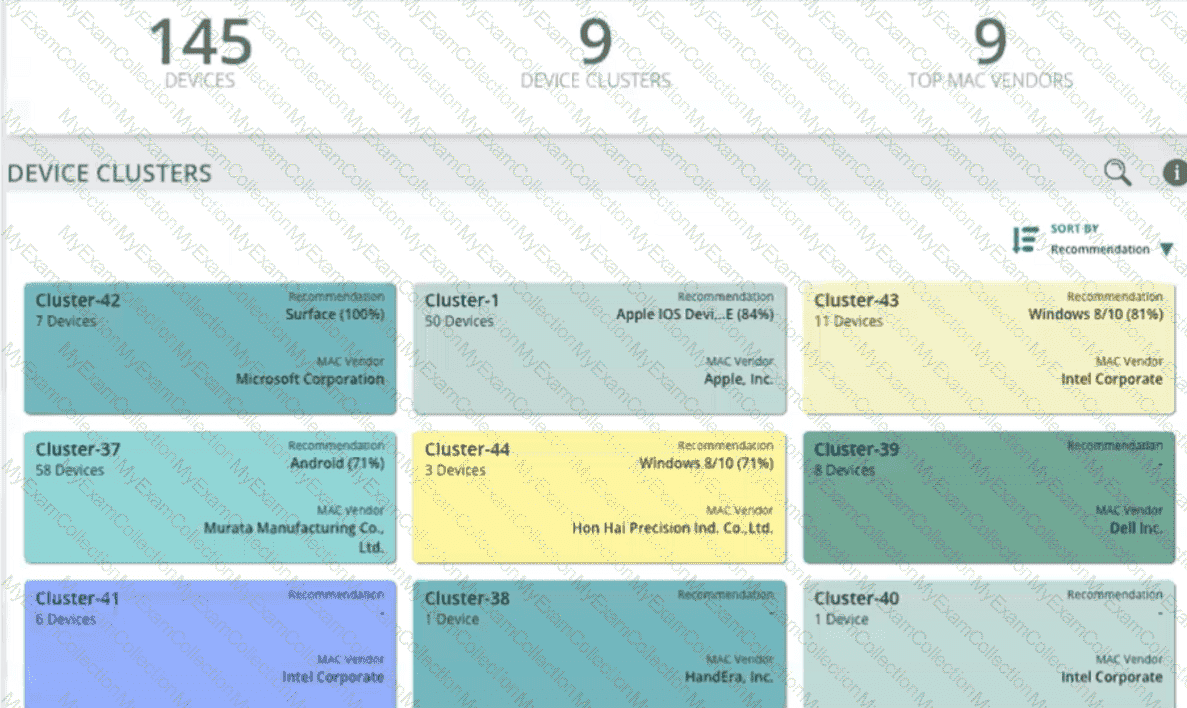
A company is using HPE Aruba Networking ClearPass Device Insight (CPDI) (the standalone application). In the CPDI interface, you go to the Generic Devices
page and see the view shown in the exhibit.
What correctly describes what you see?
What information can admins view in an AOS-CX switch’s Analytics Dashboard?
A company wants HPE Aruba Networking ClearPass Policy Manager (CPPM) to respond to Syslog messages from its Palo Alto Next Generation Firewall (NGFW)
by quarantining clients involved in security incidents.
Which step must you complete to enable CPPM to process the Syslogs properly?
A company has AOS-CX switches and HPE Aruba Networking APs, which run AOS-10 and bridge their SSIDs. Company security policies require 802.1X on all edge ports, some of which connect to APs. How should you configure the auth-mode on AOS-CX switches?
A company wants to implement Virtual Network based Tunneling (VNBT) on a particular group of users and assign those users to an overlay network with VNI
3000.
Assume that an AOS-CX switch is already set up to:
. Implement 802.1X to HPE Aruba Networking ClearPass Policy Manager (CPPM)
. Participate in an EVPN VXLAN solution that includes VNI 3000
Which setting should you configure in the users ' AOS-CX role to apply VNBT to them when they connect?
HPE Aruba Networking ClearPass Device Insight (CPDI) could not classify some endpoints using system and user rules. Using machine learning, it did assign those endpoints to a cluster and discover a recommendation. In which of these circumstances does CPDI automatically classify the endpoints based on that recommendation?
A company is implementing a client-to-site VPN based on tunnel-mode IPsec.
Which devices are responsible for the IPsec encapsulation?
You want to examine the applications that a device is using and look for any changes in application usage over several different ranges. In which HPE Aruba Networking solution can you view this information in an easy-to-view format?
You are helping an organization deploy HPE Aruba Networking SSE. What is one reason to recommend that the company install agents on remote users ' devices?
You have configured an AOS-CX switch to implement 802.1X on edge ports. Assume ports operate in the default auth-mode. VoIP phones are assigned to the " voice " role and need to send traffic that is tagged for VLAN 12. Where should you configure VLAN 12?
Which issue can an HPE Aruba Networking Secure Web Gateway (SWG) solution help customers address?
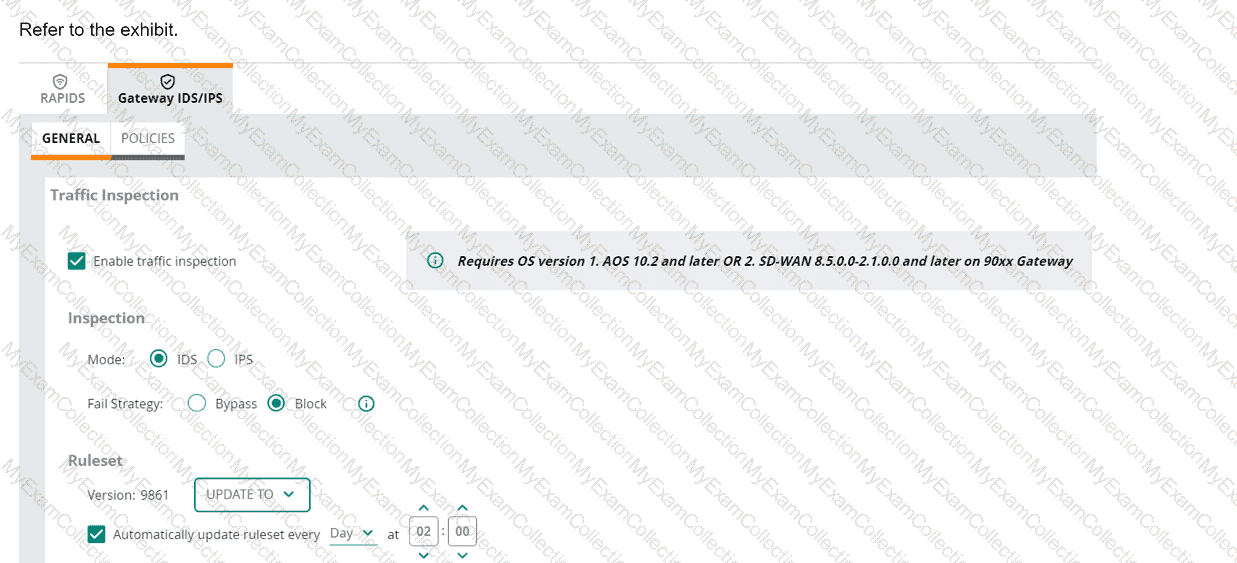
(Note that the HPE Aruba Networking Central interface shown here might look slightly different from what you see in your HPE Aruba Networking Central
interface as versions change; however, similar concepts continue to apply.)
An HPE Aruba Networking 9x00 gateway is part of an HPE Aruba Networking Central group that has the settings shown in the exhibit. What would cause the
gateway to drop traffic as part of its IDPS settings?
You manage AOS-10 APs with HPE Aruba Networking Central. A role is configured on these APs with these rules (in order):
Allow UDP on port 67 to any destination
Allow any to network 10.1.4.0/23
Deny any to network 10.1.0.0/18 + log
Deny any to network 10.0.0.0/8
Allow any to any destination
You add this new rule immediately before rule 4:
Deny SSH to network 10.1.0.0/21 + denylist
After this change, what happens when a client assigned to this role sends SSH traffic to 10.1.7.12?
HPE Aruba Networking Central displays an alert about an Infrastructure Attack that was detected. You go to the Security > RAPIDS events and see that the attack
was " Detect adhoc using Valid SSID. "
What is one possible next step?
Which use case is fulfilled by applying a time range to a firewall rule on an AOS device?
What is a use case for running periodic subnet scans on devices from HPE Aruba Networking ClearPass Policy Manager (CPPM)?
A company is using HPE Aruba Networking Central SD-WAN Orchestrator to establish a hub-spoke VPN between branch gateways (BGWs) at 1164 site and VPNCs at multiple data centers. What is part of the configuration that admins need to complete?
A ClearPass Policy Manager (CPPM) service includes these settings:
Role Mapping Policy:
Evaluate: Select first
Rule 1 conditions:
Authorization:AD:Groups EQUALS Managers
Authentication:TEAP-Method-1-Status EQUALS Success
Rule 1 role: manager
Rule 2 conditions:
Authentication:TEAP-Method-1-Status EQUALS Success
Rule 2 role: domain-comp
Default role: [Other]
Enforcement Policy:
Evaluate: Select first
Rule 1 conditions:
Tips Role EQUALS manager AND Tips Role EQUALS domain-comp
Rule 1 profile list: domain-manager
Rule 2 conditions:
Tips Role EQUALS manager
Rule 2 profile list: manager-only
Rule 3 conditions:
Tips Role EQUALS domain-comp
Rule 3 profile list: domain-only
Default profile: [Deny access]
A client is authenticated by the service. CPPM collects attributes indicating that the user is in the Contractors group, and the client passed both TEAP methods.
Which enforcement policy will be applied?
A company has been running Gateway IDS/IPS on its gateways in IDS mode for several weeks. The company wants to transition to IPS mode.
What is one step you should recommend?
A company wants to turn on Wireless IDS/IPS infrastructure and client detection at the high level on HPE Aruba Networking APs. The company does not want to
enable any prevention settings.
What should you explain about HPE Aruba Networking recommendations?
You have created this rule in an HPE Aruba Networking ClearPass Policy Manager (CPPM) service ' s enforcement policy: IF Authorization [Endpoints Repository]
Conflict EQUALS true THEN apply " quarantine_profile "
What information can help you determine whether you need to configure cluster-wide profiler parameters to ignore some conflicts?
Refer to the exhibit.
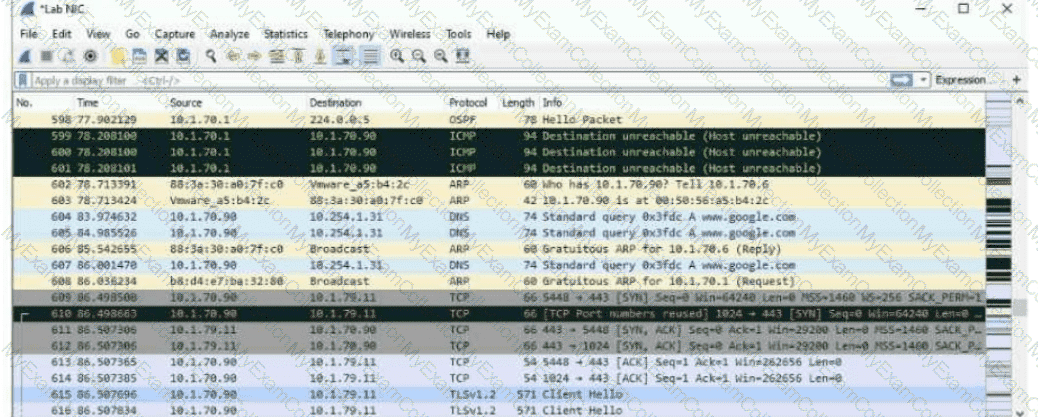
The exhibit shows a saved packet capture, which you have opened in Wireshark. You want to focus on the complete conversation between 10.1.70.90 and 10.1.79.11 that uses source port 5448.
What is a simple way to do this in Wireshark?
You need to create a rule in an HPE Aruba Networking ClearPass Policy Manager (CPPM) role mapping policy that references a ClearPass Device Insight Tag. Which Type (namespace) should you specify for the rule?

