A company discovered that numerous computers from multiple geographic locations are sending a very high number of connection requests which is causing the company’s web server to become unavailable to the general public. Which of the following attacks is occurring?
Which of the following is a data security standard for protecting credit cards?
Which of the following is the MOST basic version of Windows that includes BitLocker?
A user is attempting to browse the internet using Internet Explorer. When trying to load a familiar web page, the user is unexpectedly redirected to an unfamiliar website. Which of the following would MOST likely solve the issue?
A user has a license for an application that is in use on a personal home laptop. The user approaches a systems administrator about using the same license on
multiple computers on the corporate network. Which of the following BEST describes what the systems administrator should tell the user?
A company is looking lot a solution that provides a backup for all data on the system while providing the lowest impact to the network. Which of the following backup types will the company MOST likely select?
The findings from a security audit indicate the risk of data loss from lost or stolen laptops is high. The company wants to reduce this risk with minimal impact to users who want to use their laptops when not on the network. Which of the following would BEST reduce this risk for Windows laptop users?
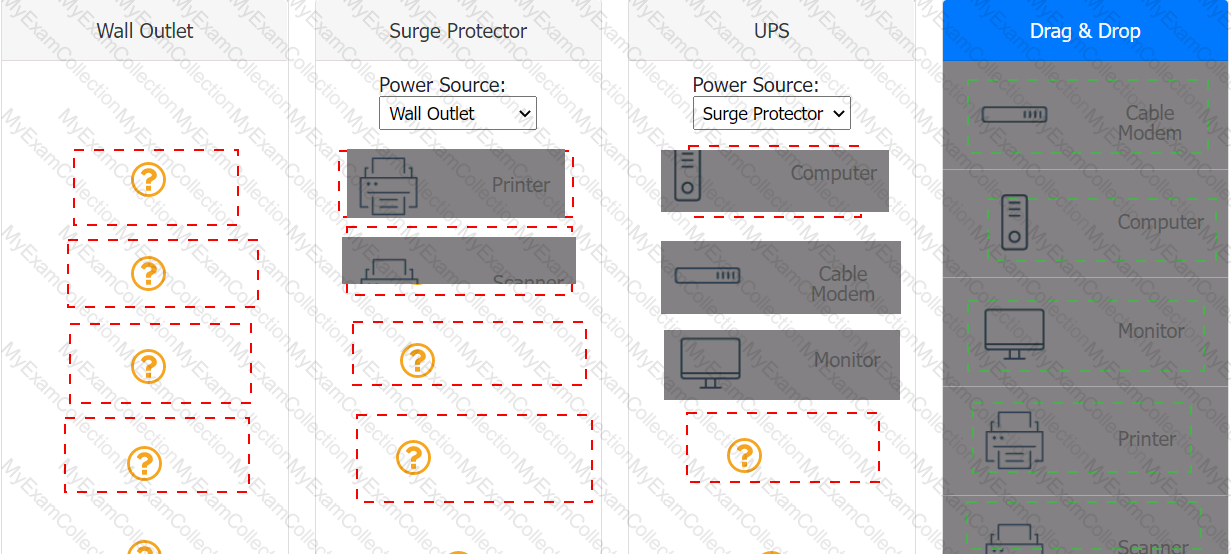
A customer recently experienced a power outage at a SOHO. The customer does not think the components are connected properly. A print job continued running for several minutes after the power failed, but the customer was not able to interact with the computer. Once the UPS stopped beeping, all functioning devices also turned off. In case of a future power failure, the customer wants to have the most time available to save cloud documents and shut down the computer without losing any data.
A Microsoft Windows PC needs to be set up for a user at a targe corporation. The user will need access to the corporate domain to access email and shared drives. Which of the following versions of Windows would a technician MOST likely deploy for the user?
A user is receiving repeated pop-up advertising messages while browsing the internet. A malware scan Is unable to locate the source of an infection. Which of the following should the technician check NEXT?
A technician has an external SSD. The technician needs to read and write to an external SSD on both Macs and Windows PCs. Which of the following filesystems is supported by both OS types?
A user receives a notification indicating the data plan on the user's corporate phone has reached its limit. The user has also noted the performance of the phone is abnormally slow. A technician discovers a third-party GPS application was installed on the phone. Which of the following is the MOST likely cause?
A laptop user is visually impaired and requires a different cursor color. Which of the following OS utilities is used to change the color of the cursor?
An analyst needs GUI access to server software running on a macOS server. Which of the following options provides the BEST way for the analyst to access the macOS server from the Windows workstation?
In which of the following scenarios would remote wipe capabilities MOST likely be used? (Select TWO).
A new service desk is having a difficult time managing the volume of requests. Which of the following is the BEST solution for the department?
A technician needs to ensure that USB devices are not suspended by the operating system Which of the following Control Panel utilities should the technician use to configure the setting?
A systems administrator notices that a server on the company network has extremely high CPU utilization. Upon further inspection, the administrator sees that the server Is consistently communicating with an IP address that is traced back to a company that awards digital currency for solving hash algorithms. Which of the following was MOST likely used to compromise the server?
A technician is setting up a new laptop. The company's security policy states that users cannot install virtual machines. Which of the following should the technician implement to prevent users from enabling virtual technology on their laptops?
A remote user is having issues accessing an online share. Which of the following tools would MOST likely be used to troubleshoot the Issue?
A technician receives a help desk ticket from a user who is unable to update a phone. The technician investigates the issue and notices the following error message: Insufficient storage space
While analyzing the phone, the technician does not discover any third-party' applications or photos. Which of the following is the best way to resolve the issue?
A user requires a drive to be mapped through a Windows command line. Which of the following command-line tools can be utilized to map the drive?
A workstation is displaying a message indicating that a user must exchange cryptocurrency for a decryption key. Which of the following is the best way for a technician to return the device to service safely?
A technician needs to establish a remote access session with a user who has a Windows workstation. The session must allow for simultaneous viewing of the workstation by both the user and technician. Which of the following remote access technologies should be used?
A desktop technician has received reports that a user's PC is slow to load programs and saved files. The technician investigates and discovers an older HDD with adequate free space. Which of the following should the technician use to alleviate the issue first?
A help desk technician determines a motherboard has failed. Which of the following is the most logical next step in the remediation process?
A large university wants to equip all classrooms with high-definition IP videoconferencing equipment. Which of the following would most likely be impacted in this situation?
A user contacts the help desk to request assistance with a program feature. The user is in a different building but on the same network as the help desk technician. Which of the following should the technician use to assist the user?
A technician has been tasked with troubleshooting audiovisual issues in a conference room. The meeting presenters are unable to play a video with sound. The following error is received:
The Audio Driver is not running.
Which of the following will MOST likely resolve the issue?
A user's corporate laptop with proprietary work Information was stolen from a coffee shop. The user togged in to the laptop with a simple password. and no other security mechanisms were in place. Which of the following would MOST likely prevent the stored data from being recovered?
The battery life on an employee's new phone seems to be drastically less than expected, and the screen stays on for a very long time after the employee sets the phone down. Which of the following should the technician check first to troubleshoot this issue? (Select two).
A technician is installing RAM in a new workstation and needs to protect against electrostatic discharge. Which of the following will best resolve this concern?
A user is unable to access a web-based application. A technician verifies the computer cannot access any web pages at all. The computer obtains an IP address from the DHCP server. Then, the technician verifies the user can ping localhost. the gateway, and known IP addresses on the interne! and receive a response. Which of the following Is the MOST likely reason tor the Issue?
A technician received a call from a user who clicked on a web advertisement Now. every time the user moves the mouse, a pop-up display across the monitor. Which of the following procedures should the technician perform?
A small-office customer needs three PCs to be configured in a network with no server. Which of the following network types is the customer's BEST choice for this environment?
A user opened a ticket regarding a corporate-managed mobile device. The assigned technician notices the OS Is several versions out of date. The user Is unaware the OS version is not current because auto-update is turned on. Which of the following is MOST likely the cause of the Issue?
Which of the following would most likely be used in a small office environment?
A systems administrator is experiencing Issues connecting from a laptop to the corporate network using PKI. Which to the following tools can the systems administrator use to help remediate the issue?
Sensitive data was leaked from a user's smartphone. A technician discovered an unapproved application was installed, and the user has full access to the device's command shell. Which of the following is the NEXT step the technician should take to find the cause of the leaked data?
Which of the following would cause a corporate-owned iOS device to have an Activation Lock issue?
Which of The following refers to the steps to be taken if an Issue occurs during a change Implementation?
A company is transitioning to a new firewall and discovers that one of the servers is still sending traffic to the old firewall. Which of the following IP address settings should a technician change to resolve this issue?
Which of the following protects a mobile device against unwanted access when it is left unattended?
Windows updates need to be performed on a department's servers. Which of the following methods should be used to connect to the server?
A Windows administrator is creating user profiles that will include home directories and network printers for several new users. Which of the following is the most efficient way for the technician to complete this task?
A systems administrator is monitoring an unusual amount of network traffic from a kiosk machine and needs to Investigate to determine the source of the traffic. Which of the following tools can the administrator use to view which processes on the kiosk machine are connecting to the internet?
A remote user is experiencing issues with Outlook settings and asks a technician to review the settings. Which of the following can the technician use to access the user's computer remotely?
A user is unable to access files on a work PC after opening a text document. The text document was labeled "URGENT PLEASE READ.txt - In active folder, .txt file titled urgent please read". Which of the following should a support technician do FIRST?
A technician discovers user input has been captured by a malicious actor. Which of the following malware types is MOST likely being used?
A systems administrator needs to access a hypervisor that went offline. After doing a port scan, the administrator notices that company policy is blocking the RDP default port. Which of the following ports should the administrator use to access the machine?
After a recent mobile OS upgrade to a smartphone, a user attempts to access their corporate email, but the application does not open. A technician restarts the smartphone, but the issue persists. Which of the following is the most likely way to resolve the issue?
Employees want their Windows 10 laptops to wirelessly connect when they take them home. Which of the following should the employees configure so the laptops can automatically connect wirelessly?
Which of the following methods is a way to superficially delete files on a hard drive?
Which of the following physical security controls can prevent laptops from being stolen?
Which of the following languages would a technician most likely use to automate the setup of various services on multiple systems?
A user is attempting to access a shared drive from a company-issued laptop while working from home. The user is unable to access any files and notices a red X next to each shared drive. Which of the following needs to be configured in order to restore the user's access to the shared drives?
Which of the following file types should be used to install software on a macOS computer? (Select two).
A technician runs a command and gets the following output:
Ethernet adapter Ethernet 3:
Connection-specific DNS Suffix . :reddog.microsoft.com
Link-local IPv6 Address .......... :fe80::de3d:9283:4f00:856a%5
IPv4 Address.......................:10.203.10.16
Subnet Mask ...................... :255.255.255.0
Default Gateway .................. :10.203.10.1
Which of the following commands did the technician use?
Which of the following applications allows a user to create backups in macOS?
Which of the following provides disk encryption on computers running a Windows OS?
A Windows 10 computer is not installing updates and continues to receive errors even during manual update installations. Which of the following should a technician do to fix the issues? (Select two).
A user in a SOHO asks an off-site, remote technician to connect securely to the user’s laptop. The technician is able to connect to the VPN but is unable to connect to the user’s laptop. Which of the following settings should the technician review?
A Windows user wants a filesystem that protects confidential data from attackers who have physical access to the system. Which of the following should the user choose?
A technician is troubleshooting a connectivity issue and wants to verify that traffic is flowing to the correct upstream locations. Which of the following commands should the technician use?
Users access files in the department share. When a user creates a new subfolder, only that user can access the folder and Its files. Which of the following will MOST likely allow all users to access the new folders?
Several computers have been infected with malware, causing the company network to slow down and sensitive company information to be lost. The IT department installs new antivirus software to remove the malware and needs to decide the best method to prevent future malware infections. Which of the following methods would be the most effective?
Which of the following is the most practical method to reduce the number of clicks on phishing emails for a public-facing organization?
A user needs to test several software replacement possibilities. Part of the process involves installing the different software options on a corporate-imaged sandboxed PC. Which of the following is the best option to allow the user to install the required software?
An employee utilizes a personal smartphone to work remotely. The employee is unable to reach the portal using the company-provided VPN service. Which of the following describes the cause of the issue?
After a user recently installs a new scanner and the associated software on a computer, they notice the computer is now starting up very slowly. Which of the following is the best tool to troubleshoot this issue?
A technician is setting up a wireless network in a small, crowded office and wants to minimize Wi-Fi access. Which of the following security settings should the technician enable?
A user identified that a program installed in a workstation does not have optional features enabled. Which of the following must the technician do to install the optional features?
A technician is updating the OS on a number of Windows workstations. After successfully updating several workstations, the technician receives an error indicating that the upgrade takes more space than is available on one of the PCs. Which of the following should the technician do to proceed with the upgrade? (Select two).
When a user is in the office, web pages are loading slowly on the user's phone. Which of the following best explains this issue?
A user calls the help desk to report an issue with their smartphone. After the user returns from a business trip, the user is no longer able to access email or visit websites without a Wi-Fi connection on the smartphone. Which of the following could the user do to most likely resolve the issue?
A technician is manually updating Windows workstations. Each workstation is currently running Windows Pro in a workgroup environment. Which of the following changes can the technician make to create a more manageable environment?
A company executive is currently attending a major music festival with a large number of attendees and is having trouble accessing a work email account. The email application is not downloading emails and appears to be stuck during connection attempts. Which of the following is most likely causing the disruption?
A technician, who is completing hardware upgrades at a company, is approached by a user who submitted a computer upgrade request. After checking the list of offices to upgrade, the technician finds that the user's office is not listed for an upgrade. Which of the following actions should the technician take next?
A technician is trying to perform an in-place upgrade of a Windows OS from a file. When the technician double-clicks the file, the technician receives a prompt to mount a drive. Which of the following file types did the technician download?
A technician is setting up a conference room computer with a script that boots the application on login. Which of the following would the technician use to accomplish this task? (Select TWO).
After a computer upgrade at an imaging lab. the upgraded computers are not able to obtain an IP address. Which of the following is most likely the issue?
Which of the following types of malware is designed to enable administrative access to a computer?
A change management review board denied an administrator's request for change. The administrator had provided the purpose and scope of the change, the date and time, and impacted systems with the risk analysis. Which of the following should be included to approve this change?
A technician installed Windows 10 on a workstation. The workstation only has 3.5GB of usable RAM, even though the technician installed 8GB. Which of the following is the MOST likely reason this system is not utilizing all the
available RAM?
A new employee was hired recently. Which of the following documents will the new employee need to sign before being granted login access to the network?
Which of the following script types is used with the Python language by default?
After a company installed a new SOHO router customers were unable to access the company-hosted public website. Which of the following will MOST likely allow customers to access the website?
A user has been unable to receive emails or browse the internet from a smartphone while traveling. However, text messages and phone calls are working without issue. Which of the following should a support technician check FIRST?
A technician is troubleshooting a mobile device that was dropped. The technician finds that the screen (ails to rotate, even though the settings are correctly applied. Which of the following pieces of hardware should the technician replace to resolve the issue?
A user is no longer able to start the OS on a computer and receives an error message indicating there is no OS found. A technician reviews the audit logs and notes that the user's system posted a S.M.A.R.T. error just days before this issue. Which of the following is the MOST likely cause of this issue?
An IT security team is implementing a new Group Policy that will return a computer to the login after three minutes. Which of the following BEST describes the change in policy?
A technician needs to provide recommendations about how to upgrade backup solutions for a site in an area that has frequent hurricanes and an unstable power grid. Which of the following should the technician recommend implementing?
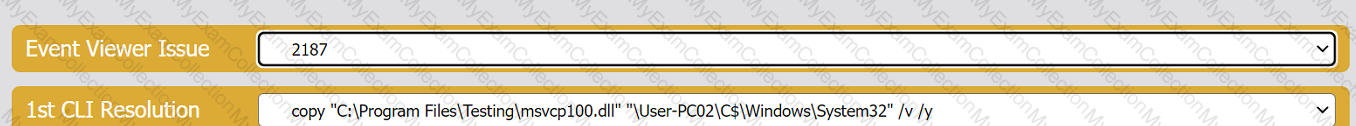
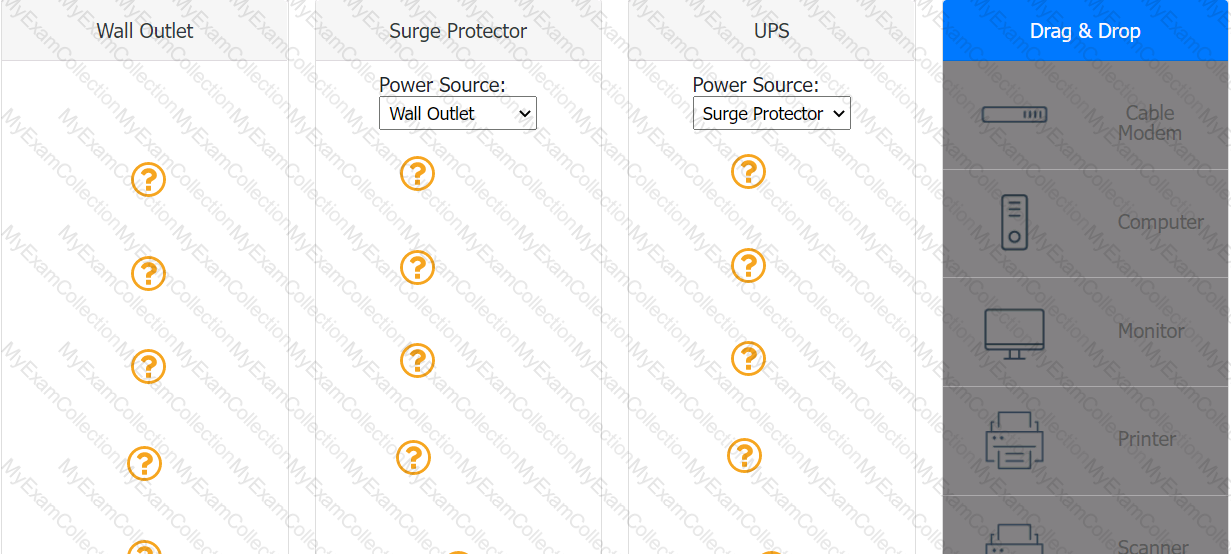
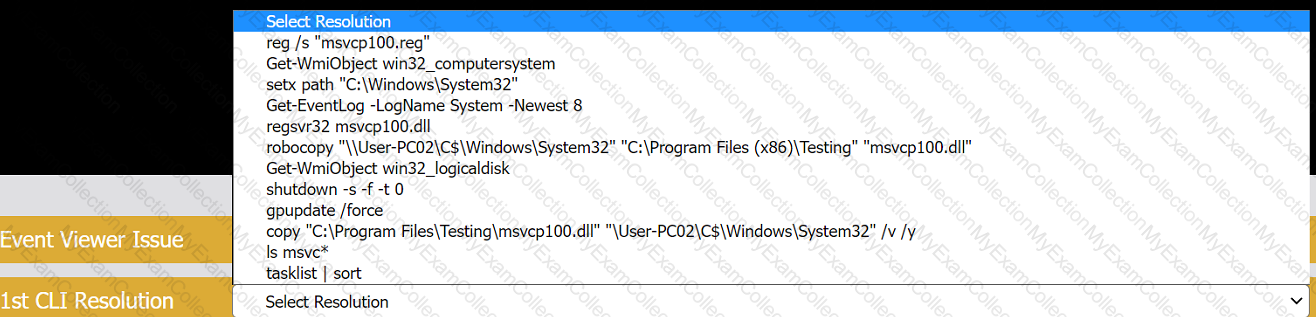
A user reports that after a recent software deployment to upgrade applications, the user can no longer use the Testing program.
However, other employees can successfully use the Testing program.
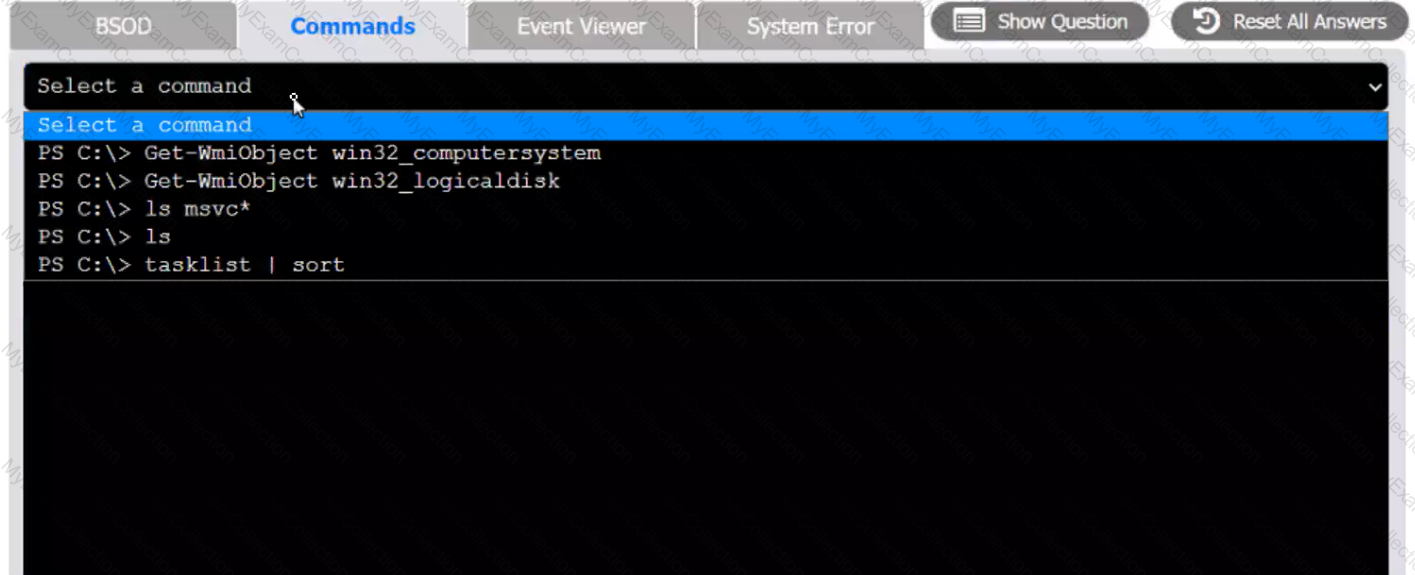
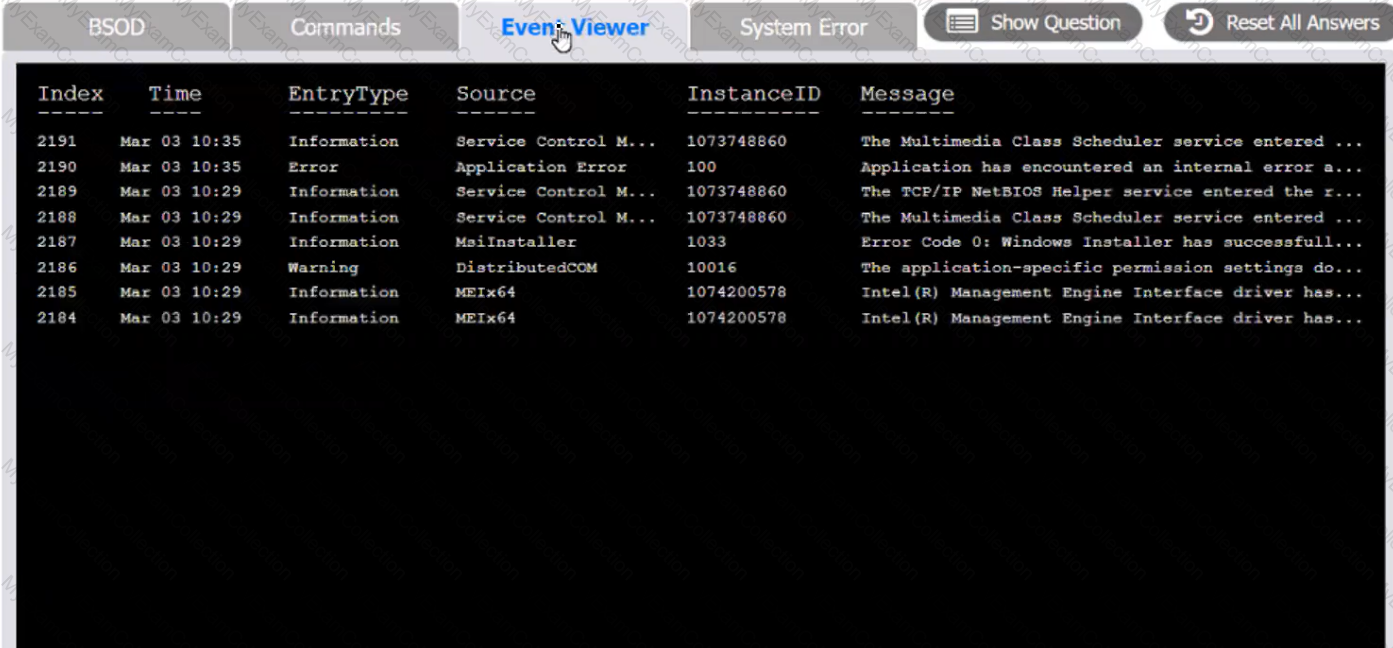
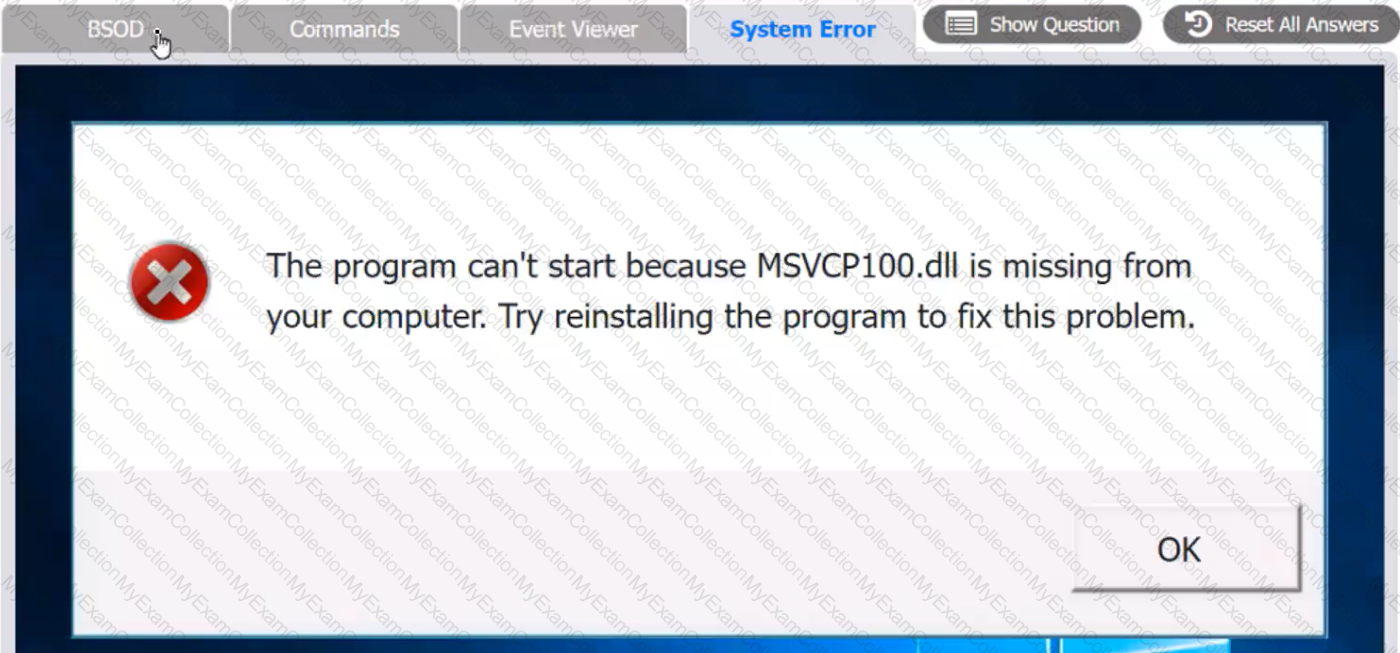
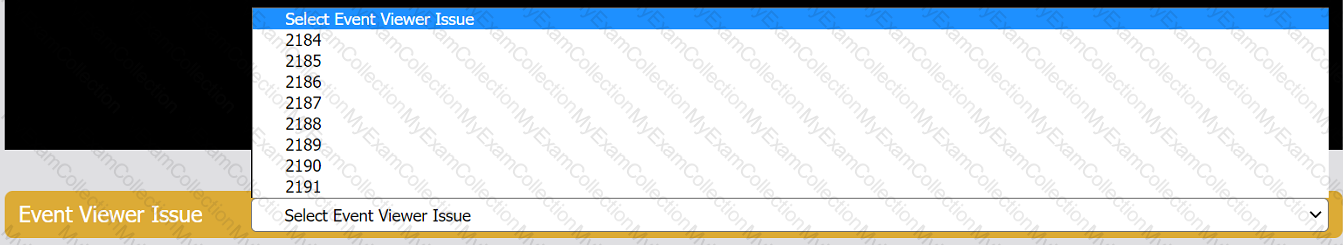
INSTRUCTIONS
Review the information in each tab to verify the results of the deployment and resolve any issues discovered by selecting the:
Index number of the Event Viewer issue
First command to resolve the issue
Second command to resolve the issue
BSOD
Commands:
Event Viewer:
System Error:
A homeowner recently moved and requires a new router for the new ISP to function correctly. The internet service has been installed and has been confirmed as functional. Which of the following is the FIRST step the homeowner should take after installation of all relevant cabling and hardware?
A technician is securing a new Windows 10 workstation and wants to enable a Screensaver lock. Which of the following options in the Windows settings should the technician use?
A user receives a call from someone who claims to be from the user's bank and requests information to ensure the user's account is safe. Which of the following social-engineering attacks is the user experiencing?
A Windows workstation that was recently updated with approved system patches shut down instead of restarting. Upon reboot, the technician notices an alert stating the workstation has malware in the root OS folder. The technician promptly performs a System Restore and reboots the workstation, but the malware is still detected. Which of the following BEST describes why the system still has malware?
A Windows user recently replaced a computer The user can access the public internet on the computer; however, an internal site at https7/companyintranet.com:8888 is no longer loading. Which of the following should a technician adjust to resolve the issue?
A user rotates a cell phone horizontally to read emails, but the display remains vertical, even though the settings indicate autorotate is on. VT1ich of the following will MOST likely resolve the issue?
Which of the following would MOST likely be used to change the security settings on a user's device in a domain environment?
A technician installed Windows 10 on a workstation. The workstation only has 3.5GB of usable RAM, even though the technician installed 8GB. Which of the following is the MOST likely reason this system is not utilizing all the available RAM?
A technician needs to transfer a file to a user's workstation. Which of the following would BEST accomplish this task utilizing the workstation's built-in protocols?
Which of the following often uses an SMS or third-party application as a secondary method to access a system?
A kiosk, which is running Microsoft Windows 10, relies exclusively on a numeric keypad to allow customers to enter their ticket numbers but no other information. If the kiosk is idle for four hours, the login screen locks. Which of the following sign-on options would allow any employee the ability to unlock the kiosk?
A systems administrator is creating a new document with a list of the websites that users are allowed to access. Which of the following types of documents is the administrator MOST likely creating?
Which of the following editions of Windows 10 requires reactivation every 180 days?
Which of the following filesystem formats would be the BEST choice to ensure read and write compatibility of USB flash drives across several generations of Microsoft operating systems?
A user's corporate phone was stolen, and the device contains company trade secrets. Which of the following technologies should be implemented to mitigate this risk? (Select TWO).
A user notices a small USB drive is attached to the user's computer after a new vendor visited the office. The technician notices two files named grabber.exe and output.txt. Which of the following attacks is MOST likely occurring?
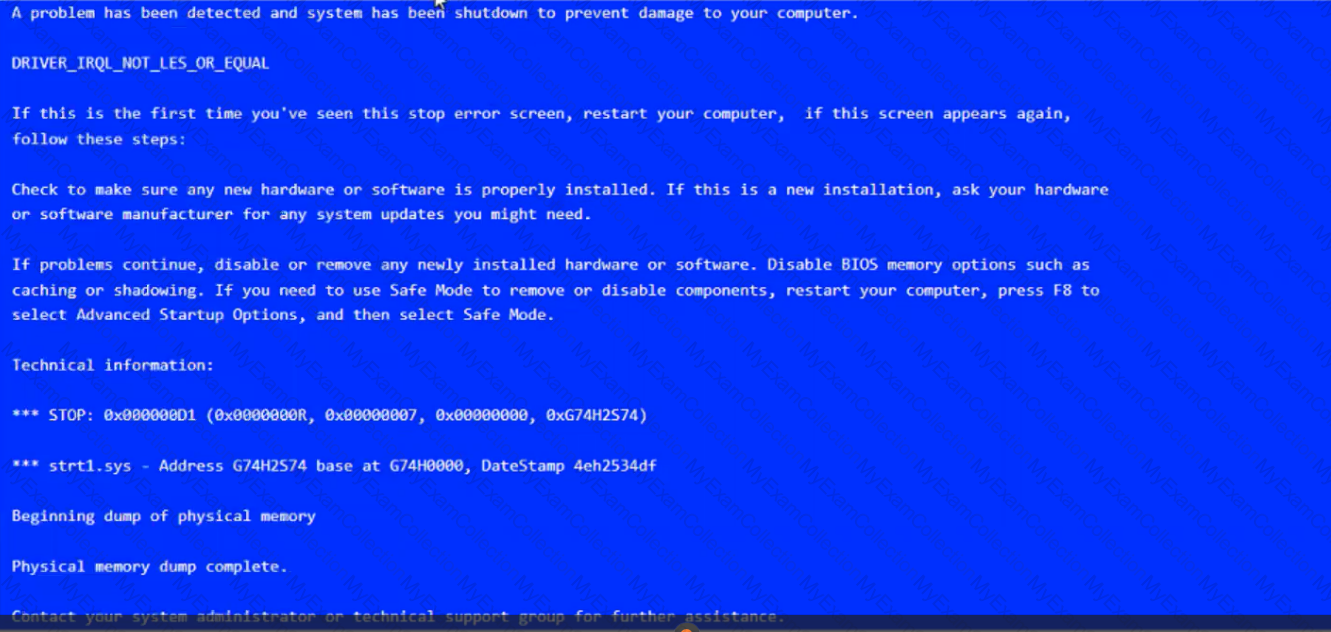
A BSOD appears on a user's workstation monitor. The user immediately presses the power button to shut down the PC, hoping to repair the issue. The user then restarts the PC, and the BSOD reappears, so the user contacts the help desk. Which of the following should the technician use to determine the cause?
Which of the following features allows a technician to configure policies in a Windows 10 Professional desktop?
A user reports that the pages flash on the screen two or three times before finally staying open when attempting to access banking web pages. Which of the following troubleshooting steps should the technician perform NEXT to resolve the issue?
A technician is troubleshooting application crashes on a Windows workstation. Each time the workstation user tries to open a website in a browser, the following message is displayed:
crypt32.d11 is missing not found
Which of the following should the technician attempt FIRST?
A technician needs to strengthen security controls against brute-force attacks. Which of the following options best meets this requirement?
A customer who uses a Linux OS called the help desk to request assistance in locating a missing file. The customer does not know the exact name of the file but can provide a partial file name. Which of the following tools should the technician use? (Select two).
An employee using an Apple MacBook is receiving frequent, random pop-up requests from other Apple devices wanting to share photos and videos and asking whether the user would like to accept the request Which of the following configurations should the technician advise the user to change first"?
A technician downloaded an OS installation file but is unable to run it. When the technician tries to open the file, a message indicates no software is installed to run this file. Which of the following should the technician do next to attempt to access the OS file?
A technician is troubleshooting a user’s PC that is displaying pop-up windows, which are advertising free software downloads. When the technician tries to open a document, the system displays an error message that reads: Not enough memory to perform this operation. Which of the following should be the technician's next step to resolve this issue?
A user’s Windows 10 workstation with an HDD is running really slowly. The user has opened, closed, and saved many large files over the past week. Which of the following tools should a technician use to remediate the issue?
A user receives an error message on a Windows 10 device when trying to access a mapped drive from a Windows XP machine in the office. Other Windows XP devices in the office can access the drive. Which of the following Control Panel utilities should the user select to enable connectivity to the device?
A technician wants to improve password security after several users admitted to using very simple passwords. Which of the following is the best way to resolve this issue?
A company using Active Directory wants to change the location of all users' "Documents" to a file server on the network. Which of the following should the company set up to accomplish this task?
A technician needs to configure a computer for a user to work from home so the user can still securely access the user’s shared files and corporate email. Which of the following tools would best accomplish this task*?
A customer service representative is unable to send jobs to a printer at a remote branch office. However, the representative can print successfully to a local network printer. Which of the following commands should a technician use to view the path of the network traffic from the PC?
A user submits a request to have a graphics application installed on a desktop When the technician attempts to install the application, the installation fails and the error message "Not compatible with OS' is displayed. Which of the following is the most likely reason for this error message?
A technician receives a high-priority ticket about sensitive information collected from an end user’s workstation. Which of the following steps should a technician take to preserve the chain of custody for a forensic investigation?
A user is unable to start a computer following a failed Windows 10 update. When trying to start the computer, the user sees a blue screen of death. Which of the following steps should a technician take to diagnose the issue?
A technician is upgrading the Microsoft Windows 10 OS. Which of the following are required for the technician to safely upgrade the OS? (Select two).
A company uses shared drives as part of a workforce collaboration process. To ensure the correct access permissions, inheritance at the top-level folder is assigned to each department. A manager's team is working on confidential material and wants to ensure only the immediate team can view a specific folder and its subsequent files and subfolders. Which of the following actions should the technician most likely take?
A technician is configuring a SOHO router and wants to only allow specific computers on the network. Which of the following should the technician do?
Users report having difficulty using the Windows Hello facial recognition feature. Which of the following is a secondary feature of Windows Hello that can be used to log in?
A technician is troubleshooting a smartphone that is unable to download and install the latest OS update. The technician notices the device operates more slowly than expected, even after rebooting and closing all applications. Which of the following should the technician check next?
A network administrator wants to enforce a company's security policy that prohibits USB drives on user workstations. Which of the following commands should the administrator run on the users' workstations?
A user takes a work-issued laptop home for the first time. When the user attempts to browse any website on the home internet, the user receives the following error:
"This site cannot be reached."
A technician from work confirms that the static IP that was set up on the machine was changed back to DHCP. Which of the following needs to be corrected?
A network administrator is setting up the security for a SOHO wireless network. Which of the following options should the administrator enable to secure the network?
A company installed WAPs and deployed new laptops and docking stations to all employees. The docking stations are connected via LAN cables. Users are now reporting degraded network service. The IT department has determined that the WAP mesh network is experiencing a higher than anticipated amount of traffic. Which of the following would be the most efficient way to ensure the wireless network can support the expected number of wireless users?
A technician is troubleshooting a Windows system that is having issues with the OS loading at startup. Which of the following should the technician do to diagnose the issue?
A company was recently attacked by ransomware. The IT department has remediated the threat and determined that the attack method used was email. Which of the following is the most effective way to prevent this issue from reoccurring?
An administrator needs to select a method to dispose of SSDs containing sensitive data. Which of the following are the most appropriate methods? (Select two).
A technician needs to troubleshoot a user's computer while the user is connected to the system. The technician must also connect to the user's system using remote access tools built in to Windows Which of the following is the best option to troubleshoot the user's computer?
A user's computer is running slower than usual and takes a long time to start up. Which of the following tools should the technician use first to investigate the issue?
Which of the following operating systems was the app file type designed to run under as an application file bundle?
A user's company phone has several pending software updates. A technician completes the following steps:
•Rebooted the phone
•Connected to Wi-Fi
•Disabled metered data
Which of the following should the technician do next?
A customer wants to make sure the data is protected and secure on a Windows laptop's hard drive. Which of the following is the best solution?
Malware is installed on a device after a user clicks on a link in a suspicious email. Which of the following is the best way to remove the malware?
A systems administrator is troubleshooting network performance issues in a large corporate office. The end users report that traffic to certain internal environments is not stable and often drops. Which of the following command-line tools can provide the most detailed information for investigating the issue further?
A malicious user was able to export an entire website's user database by entering specific commands into a field on the company's website. Which of the following did the malicious user most likely exploit to extract the data?
A technician is setting up a network printer for a customer who has a SOHO router. The technician wants to make sure the printer stays connected in the future and is available on all the computers in the house. Which of the following should the technician configure on the printer?
Which of the following file types allows a user to easily uninstall software from macOS by simply placing it in the trash bin?
.exe
Which of the following is the most likely reason a filtration system is critical for data centers?
A user's computer unexpectedly shut down immediately after the user plugged in a USB headset. Once the user turned the computer back on, everything was functioning properly, including the headset. Which of the following Microsoft tools would most likely be used to determine the root cause?
A technician wants to install Developer Mode on a Windows laptop but is receiving a "failed to install package" message. Which of the following should the technician do first?
A technician needs to replace a PC's motherboard. The technician shuts down the PC. Which of the following steps should the technician take next?
Which of the following are mobile operating systems used on smartphones? (Select two).
A company-owned mobile device is displaying a high number of ads, receiving data-usage limit notifications, and experiencing slow response. After checking the device, a technician notices the device has been jailbroken. Which of the following should the technician do next?
Run an antivirus and enable encryption.
Which of the following is the best reason for sandbox testing in change management?
To evaluate the change before deployment
A computer technician is investigating a computer that is not booting. The user reports that the computer was working prior to shutting it down last night. The technician notices a removable USB device is inserted, and the user explains the device is a prize the user received in the mail yesterday. Which of the following types of attacks does this describe?
A user is unable to access a remote server from a corporate desktop computer using the appropriate terminal emulation program. The user contacts the help desk to report the issue. Which of the following clarifying questions would be most effective for the help desk technician to ask the user in order to understand the issue?
A technician was assigned a help desk ticket and resolved the issue. Which of the following should the technician update to assist other technicians in resolving similar issues?
End user training
A large company is changing its password length requirements. The Chief Information Officer is mandating that passwords now be at least 12 characters long, instead of 10. Which of the following should be used to adjust this setting?
Group Policy
A user requested that the file permissions on a Linux device be changed to only allow access to a certain group of users. Which of the following commands should be used to complete the user's request?
A customer installed a new web browser from an unsolicited USB drive that the customer received in the mail. The browser is not working as expected, and internet searches are redirected to another site. Which of the following should the user do next after uninstalling the browser?
Which of the following filesystems replaced FAT as the preferred filesystem for Microsoft Windows OS?
A technician is troubleshooting a PC because the user has reported strange pop-up windows and computer performance issues. Which of the following actions should the technician take next?
A systems administrator received a request to limit the amount of cellular data a user's Windows 10 tablet can utilize when traveling. Which of the following can the administrator do to best solve the user's issue?
Which of the following operating systems would most likely be used to run the inventory management system at a factory?
Which of the following items require special e-waste recycling? (Select two).
Solid-state drive
A technician is partitioning a hard disk. The five primary partitions should contain 4TB of free space. Which of the following partition styles should the technician use to partition the device?
A technician has verified a computer is infected with malware. The technician isolates the system and updates the anti-malware software. Which of the following should the technician do next?
An engineer is configuring a new server that requires a bare-metal installation. Which of the following installation methods should the engineer use if installation media is not available on site?
A user recently purchased a second monitor and wants to extend the Windows desktop to the new screen. Which of the following Control Panel options should a technician adjust to help the user?
Color Management
Which of the following commands can a technician use to get the MAC address of a Linux distribution?
net use
A user reports seeing random, seemingly non-malicious advertisement notifications in the Windows 10 Action Center. The notifications indicate the advertisements are coming from a web browser. Which of the following is the best solution for a technician to implement?
Which of the following is the best way to limit the loss of confidential data if an employee's company smartphone is lost or stolen?
When visiting a particular website, a user receives a message stating, "Your connection is not private." Which of the following describes this issue?
A user receives a call from someone claiming to be a technical support agent. The caller asks the user to log in to the computer.
Which of the following security measures should the user take to ensure security and privacy?
When trying to access a secure internal network, the user receives an error messaging stating, "There is a problem with this website's security certificate." The user reboots the desktop and tries to access the website again, but the issue persists. Which of the following should the user do to prevent this error from reoccurring?
A customer calls desktop support and begins yelling at a technician. The customer claims to have submitted a support ticket two hours ago and complains that the issue still has not been resolved. Which of the following describes how the technician should respond?
Place the customer on hold until the customer calms down.
A technician is moving a Windows workstation from the accounting department to the sales department and needs to update the IP and gateway settings. Which of the following Control Panel utilities should the technician use?
A user calls the help desk to report potential malware on a computer. The anomalous activity began after the user clicked a link to a free gift card in a recent email The technician asks the user to describe any unusual activity, such as slow performance, excessive pop-ups, and browser redirections. Which of the following should the technician do NEXT?
A technician needs to document who had possession of evidence at every step of the process. Which of the following does this process describe?
A technician is configuring a new Windows laptop Corporate policy requires that mobile devices make use of full disk encryption at all limes Which of the following encryption solutions should the technician choose?
A technician is setting up a desktop computer in a small office. The user will need to access files on a drive shared from another desktop on the network. Which of the following configurations should the technician employ to achieve this goal?
A user contacted the help desk to report pop-ups on a company workstation indicating the computer has been infected with 137 viruses and payment is needed to remove them. The user thought the company-provided antivirus software would prevent this issue. The help desk ticket states that the user only receives these messages when first opening the web browser. Which of the following steps would MOST likely resolve the issue? (Select TWO)
A technician wants to enable BitLocker on a Windows 10 laptop and is unable to find the BitLocker Drive Encryption menu item in Control Panel. Which of the following explains why the technician unable to find this menu item?
The Chief Executive Officer at a bark recently saw a news report about a high-profile cybercrime where a remote-access tool that the bank uses for support was also used in this crime. The report stated that attackers were able to brute force passwords to access systems. Which of the following would BEST limit the bark's risk? (Select TWO)
A user reports that a PC seems to be running more slowly than usual. A technician checks system resources, but disk, CPU, and memory usage seem to be fine. The technician sees that GPU temperature is extremely high. Which of the following types of malware is MOST likely to blame?
An executive has contacted you through the help-desk chat support about an issue with a mobile device.
Assist the executive to help resolve the issue.
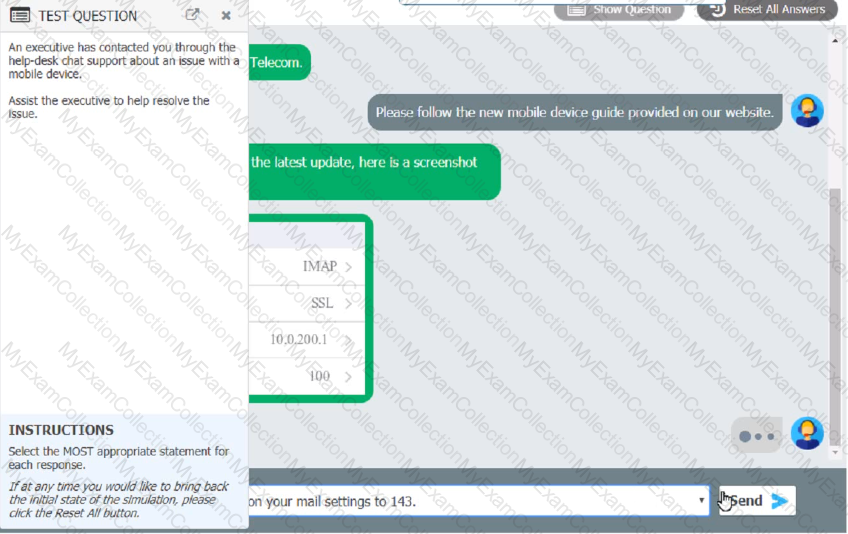
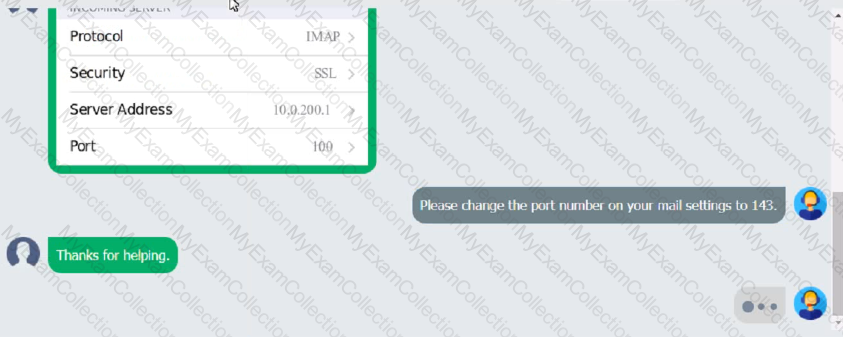
Which of the following should be done NEXT?
A user wants to set up speech recognition on a PC. In which of the following Windows Settings tools can the user enable this option?
A user attempts to open some files, but a message appears stating that the files are encrypted. The user was able to access these files before without receiving this message and no changes have been made within the company. Which of the following has infected the computer?
After clicking on a link in an email a Chief Financial Officer (CFO) received the following error:
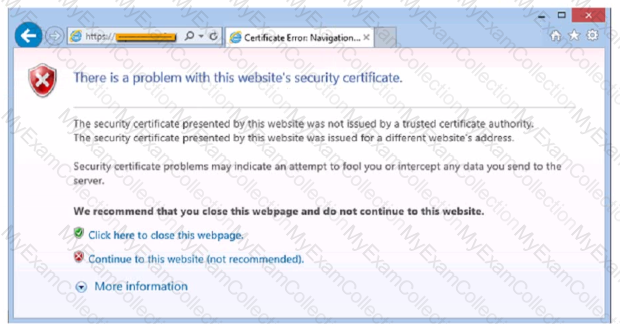
The CFO then reported the incident to a technician. The link is purportedly to the organization's bank. Which of the following should the technician perform FIRST?
A technician needs to interconnect two offices to the main branch while complying with good practices and security standards. Which of the following should the technician implement?
A technician needs to formal a USB drive to transfer 20GB of data from a Linux computer to a Windows computer. Which of the following filesystems will the technician MOST likely use?
The network was breached over the weekend System logs indicate that a single user's account was successfully breached after 500 attempts with a dictionary attack. Which of the following would BEST mitigate this threat?
A user reports that text on the screen is too small. The user would like to make the text larger and easier to see. Which of the following is the BEST way for the user to increase the size of text, applications, and other items using the Windows 10 Settings tool?
As part of a CYOD policy a systems administrator needs to configure each user's Windows device to require a password when resuming from a period of sleep or inactivity. Which of the following paths will lead the administrator to the correct settings?
A technician is replacing the processor in a desktop computer prior to opening the computer, the technician wants to ensure the internal components are protected. Which of the following safety procedures would BEST protect the components in the PC? (Select TWO).
A user is unable to use any internet-related functions on a smartphone when it is not connected to Wi-Fi When the smartphone is connected to Wi-Fi the user can browse the internet and send and receive email. The user is also able to send and receive text messages and phone calls when the smartphone is not connected to Wi-Fi. Which of the following is the MOST likely reason the user is unable to use the internet on the smartphone when it is not connected to Wi-Fi?
A user receives the following error while attempting to boot a computer.
BOOTMGR is missing
press Ctrl+Alt+Del to restart
Which of the following should a desktop engineer attempt FIRST to address this issue?
Which of the following must be maintained throughout the forensic evidence life cycle when dealing with a piece of evidence?
A user reports that the hard drive activity light on a Windows 10 desktop computer has been steadily lit for more than an hour, and performance is severely degraded. Which of the following tabs in Task Manager would contain the information a technician would use to identify the cause of this issue?
A user reports a PC is running slowly. The technician suspects it has a badly fragmented hard drive. Which of the following tools should the technician use?
A desktop specialist needs to prepare a laptop running Windows 10 for a newly hired employee. Which of the following methods should the technician use to refresh the laptop?
Upon downloading a new ISO, an administrator is presented with the following string:
59d15a16ce90cBcc97fa7c211b767aB
Which of the following BEST describes the purpose of this string?
An incident handler needs to preserve evidence for possible litigation. Which of the following will the incident handler MOST likely do to preserve the evidence?
Someone who is fraudulently claiming to be from a reputable bank calls a company employee. Which of the following describes this incident?
A user receives a notification indicating the antivirus protection on a company laptop is out of date. A technician is able to ping the user's laptop. The technician checks the antivirus parent servers and sees the latest signatures have been installed. The technician then checks the user's laptop and finds the antivirus engine and definitions are current. Which of the following has MOST likely occurred?
A user reports that a workstation is operating sluggishly Several other users operate on the same workstation and have reported that the workstation is operating normally. The systems administrator has validated that the workstation functions normally. Which of the following steps should the systems administrator most likely attempt NEXT?
A technician receives a ticket indicating the user cannot resolve external web pages However, specific IP addresses are working. Which of the following does the technician MOST likely need to change on the workstation to resolve the issue?
A technician found that an employee is mining cryptocurrency on a work desktop. The company has decided that this action violates its guidelines. Which of the following should be updated to reflect this new requirement?
When a user calls in to report an issue, a technician submits a ticket on the user's behalf. Which of the following practices should the technician use to make sure the ticket is associated with the correct user?
A technician is asked to resize a partition on the internal storage drive of a computer running macOS. Which of the followings tools should the technician use to accomplish this task?
A technician is installing new network equipment in a SOHO and wants to ensure the equipment is secured against external threats on the Internet. Which of the following actions should the technician do FIRST?
A mobile phone user has downloaded a new payment application that allows payments to be made with a mobile device. The user attempts to use the device at a payment terminal but is unable to do so successfully. The user contacts a help desk technician to report the issue. Which of the following should the technician confirm NEXT as part of the troubleshooting process?
Each time a user tries to go to the selected web search provider, a different website opens. Which of the following should the technician check FIRST?
An administrator has received approval for a change request for an upcoming server deployment. Which of the following steps should be completed NEXT?
A technician connects an additional monitor to a PC using a USB port. The original HDMI monitor is mounted to the left of the new monitor. When moving the mouse to the right from the original monitor to the new monitor, the mouse stops at the end of the screen on the original monitor. Which
of the following will allow the mouse to correctly move to the new monitor?
A user reports a workstation has been performing strangely after a suspicious email was opened on it earlier in the week. Which of the following should the technician perform FIRST?
A technician downloaded software from the Internet that required the technician to scroll through a text box and at the end of the text box, click a
button labeled Accept Which of the following agreements IS MOST likely in use?
A technician is installing a new business application on a user's desktop computer. The machine is running Windows 10 Enterprise 32-bit operating system. Which of the following files should the technician execute in order to complete the installation?